| Home │ Part II │ Merge Registry │ Reg.exe │ | |||||||
|
|
Locking and Restricting the Registry in Windows XP Part IRevised and expanded version This article applies to: Windows 2000/XP/Server 2003 Topics on this page: [1] Introduction: various types of restrictions
[3] Regedit disabled: solutions
1. Introduction: various types of restrictionsThe registry editor in Windows XP is regedit.exe, which is an enhanced version combining the old regedit.exe and regedt32.exe from Windows 2000. There are several situations when you cannot run regedit or regedt32.exe:
This is a common problem encountered in computer forums and I've experimented with locking/unlocking and restricting the registry. This article deals with scenario (2) and Part II with (3) and (4). If you just need the quick fix urgently, skip the details and go straight to the Solutions section below. Remember to remove all viruses, Trojans and browser hijack objects as well. If your Internet Explorer has been hijacked then read my articles on IE Hijack. If you are not an administrator and don't have permission to edit the registry then you should leave it alone. The following tips are for those who have permission to do so.
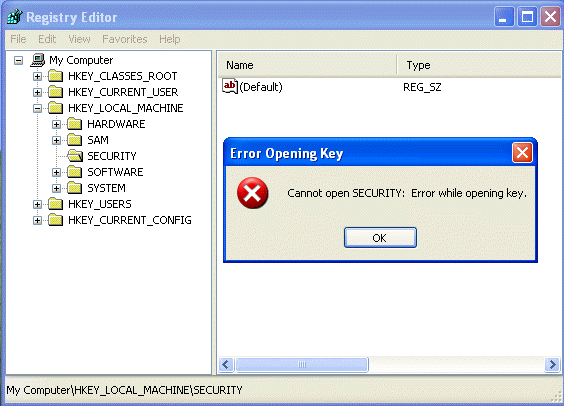
1.1. No administrative privileges: Guest or limited account usersNormally, guest and limited account users can open and edit his/her own HKCU registry hive but cannot read or edit many other keys especially the HKLM hive. They have full control of the HKCU hive but read only or no permission to the rest. If a guest tries to open a key without permission an Error Opening Key box pops up (fig. 1). The SYSTEM and Administrator group have full control to all the keys. Registry user permission is rather like NTFS folder permissions but not quite in the other categories of restriction discussed here and not to be confused with them (KB 310426).
Fig. 1. Error Opening Key error message when registry user permission is denied.
1.2. Registry editor disabledThis is the classic case and frequently encountered in computer forums. If your registry editor (regedit.exe) has been disabled you'll see this message when you attempt to run it from anywhere, including the Start, Run box, the command prompt, directly by double clicking on regedit.exe or regedt32.exe (Fig. 2):
Fig. 2. Registry Editor disabled error message
1.3. Operation cancelled due to restrictionsThis is the less often seen situation but not to be mixed up with the
previous one. Regedit can be disabled by another means, programme restriction, when
this message pops up:
Fig. 3. Restrictions error box.
2. Regedit disabled: causesBy default administrators have full control (read, write, delete) to open regedit. This can be disabled in several ways:(1) intentionally - by the administrator with Group Policy (in a
domain) or Local Computer Policy
in the Group Policy Editor: (2) inadvertently - by browser hijack objects or malicious scripts by setting the same registry key as the Group Policy Editor; or Note that running *.exe files in general can also disabled after a viral infection; this will be explained in Part II. The default registry keys have no policy key. If permission is denied the changes would be in the HKCU key (Fig. 4): HKEY_CURRENT_USER\Software\Microsoft\Windows\
Fig. 4. Regedit DisableRegistryTools key
3. Regedit disabled: solutionsFirst, determine if the problem is confined to regedit (regedit.exe), or all exe files or if it is due to operation restriction (see above). In the latter two cases, read Part II. Then read on.It is quite easy to reset the registry key provided the method does not involve running regedit itself. There is no definitive order in the list: it depends on your skills and what you have. Method 1 is generally the easiest for Windows XP Professional. For Windows XP Home edition users, use HijackThis or one of the methods in part II. Why do I give you so many methods? Because there is more than one way to do things and it's a marvellous way to learn things. Don't read everything if you can't be bothered.
Wrong and ineffective method: the old merge reg file method does not work in Windows XP - DO NOT USE THIS Let me dispel this myth once and for all: for the record, the merge reg method does NOT work in Windows XP, unlike Windows 9x. This method is frequently offered as solution in forums and is incorrect. I've tried running the following reg file (and the regedit4 version which probably works in Windows 9x) to change the settings back to (0) in Windows XP but it didn't work (KB 310516). In Windows 9x it is unnecessary to use this method anyway because it has its own System Policy Tool and a similar setting as in Windows XP's Group Policy Editor (see below). Windows Registry Editor Version 5.00
Running another reg file with a minus sign - in front of the keys to delete the values (1) didn't work either. In both cases the same denial message came up (Fig. 2 above). Note also that the HKLM registry key is not altered by the Group Policy Editor and is thus irrelevant. I include it here because it comes up a lot in forums.
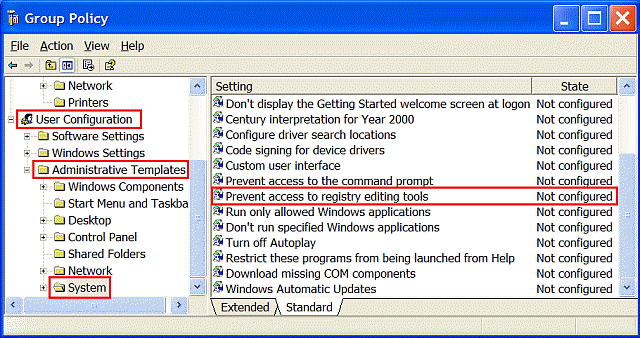
3.1. Edit Group Policy ObjectIf you have Windows XP Professional and an administrator account then you can reset the registry using the Group Policy Editor to edit the Local Group Policy Object (GPO): this changes the HKCU key only (the HKLM key is not used). If you are on a computer joined to a domain controller then edit the appropriate GPO. If you have Windows XP SP2 please read section 3.2 too.For the local computer, go to: Start, Run, gpedit.msc, navigate to: Local Computer Policy, User Configuration\Administrative Templates\System,
Fig. 5. Prevent access to registry editing tools.
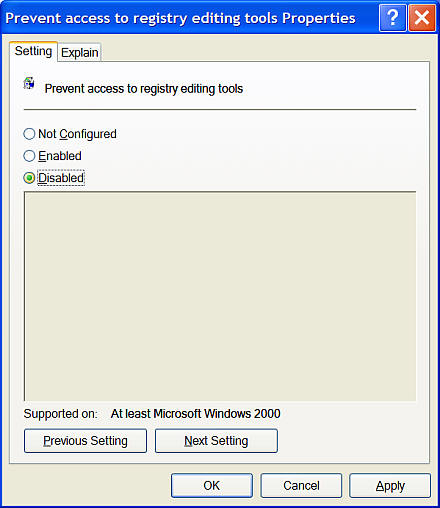
In the Setting window Choose Disabled (this would reset the value to 0 or delete the name and value if there are no other policies) or Not Configured (this would delete the name and value and is therefore preferable). Click Apply and OK (Fig. 6). The unlocking takes effect immediately.
Fig. 6. Group Policy Editor: Prevent access to registry editing tools Properties box.
3.1.1. Changes in Windows XP SP2The Group Policy template has been revised and the Group Policy Editor now shows two settings under Enabled. Enabled > Disabled regedit from running silently? > No sets the registry key value to 1, as before; Enabled > Disabled regedit from running silently? > Yes sets the DisableRegistryTools key value to 2, which is new. Setting the policy to Disabled or Not Configured deletes the policy key altogether.
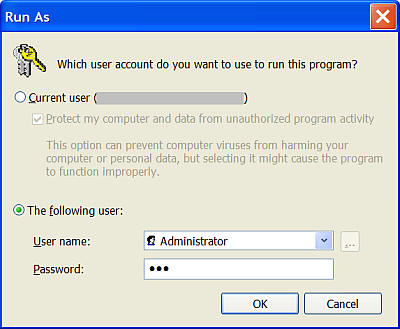
3.2. Run As: secondary Logon as AdministratorWhen you normally sit at the computer and logon as your own user account, you are the console user. When you run something with the credentials of another account you become the secondary user. To run regedit as a secondary user using the Administrator account (assuming this is not your own account), in Windows Explorer go to: %SYSTEMROOT% (usually C:\WINDOWS\); Obviously you must know the password or have permission to do this. If the Administrator account has blank password (the default in Windows XP Home edition) you will be refused.
Fig. 7. The Run As box.
Regedit opens but using a different administrator account (fig. 8). You can tell because if you examine the HKCU key in detail you'll find that it is not your own key with your customised changes.
Fig. 8. Regedit opens using another account.
Therefore do not edit the current HKCU hive but instead go to the HKEY_USERS hive: the registry key for the locked account would be in one of the pairs of S-1-5-21-{domain identifier-500} keys. The domain identifier number is unique to each account so if you don't know which one to unlock you need to open each one and find the offending entry. This process is known as secondary logon. The HKCU hive is in fact mapped to one of the HKU keys. In the registry nomenclature, the S-1-5-21-{domain identifier-500} refers to specific console user or secondary user accounts. They are usually in pairs so one of the above pairs belongs to the secondary (in this case, the root Administrator) account and the other the original console user account. Because both user's HKCU hives are loaded, you cannot use the Files, Load Hive method to load the console user hive again.
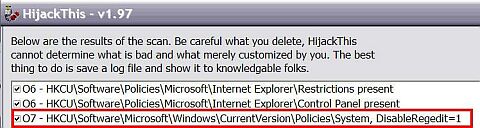
3.3. HijackThisIf you use Windows XP Home edition or are inexperienced in regedit or Group Policy this is probably the method of choice and is easy. Download HijackThis (or here) to remove the offending HKCU entry (Fig. 9). The advantage of using HijackThis is that the tool will detect and remove other hijack objects in one operation.To unlock regedit:
HijackThis will also find the HKLM\...\DisableRegedit=1 entry if present (as I found while experimenting but it is totally irrelevant): if found then remove it anyway.
Fig. 9. HijackThis scan log showing HKCU DisableRegistryTools key.
Once you have removed the entry it is worth rebooting and rescanning with HijackThis. Verify that you can now run regedit.
Go to TOP
Copyright © 2003-2005 by Kilian. All my articles including graphics are provided "as is" without warranties of any kind. I hereby disclaim all warranties with regard to the information provided. In no event shall I be liable for any damage of any kind whatsoever resulting from the information. The articles are provided in good faith and after some degree of verification but they may contain technical or typographical errors. Links to other web resources may be changed at any time and are beyond the control of the author. Articles may be added, removed, edited or improved at any time. No support is provided by the author. All the products mentioned are trademarks of their respective companies. DISCLAIMER: Edit the registry at your own risk. If possible use the Group Policy Editor. There is no undo in regedit. If you are inexperienced with regedit, when possible back up the whole registry or the key you are about to change first before modifying or deleting the key. Do not modify more than one key/name/value at a time. Re-logon or reboot and see what happens first. Last updated 12 Apr 2005 |
|
|||||